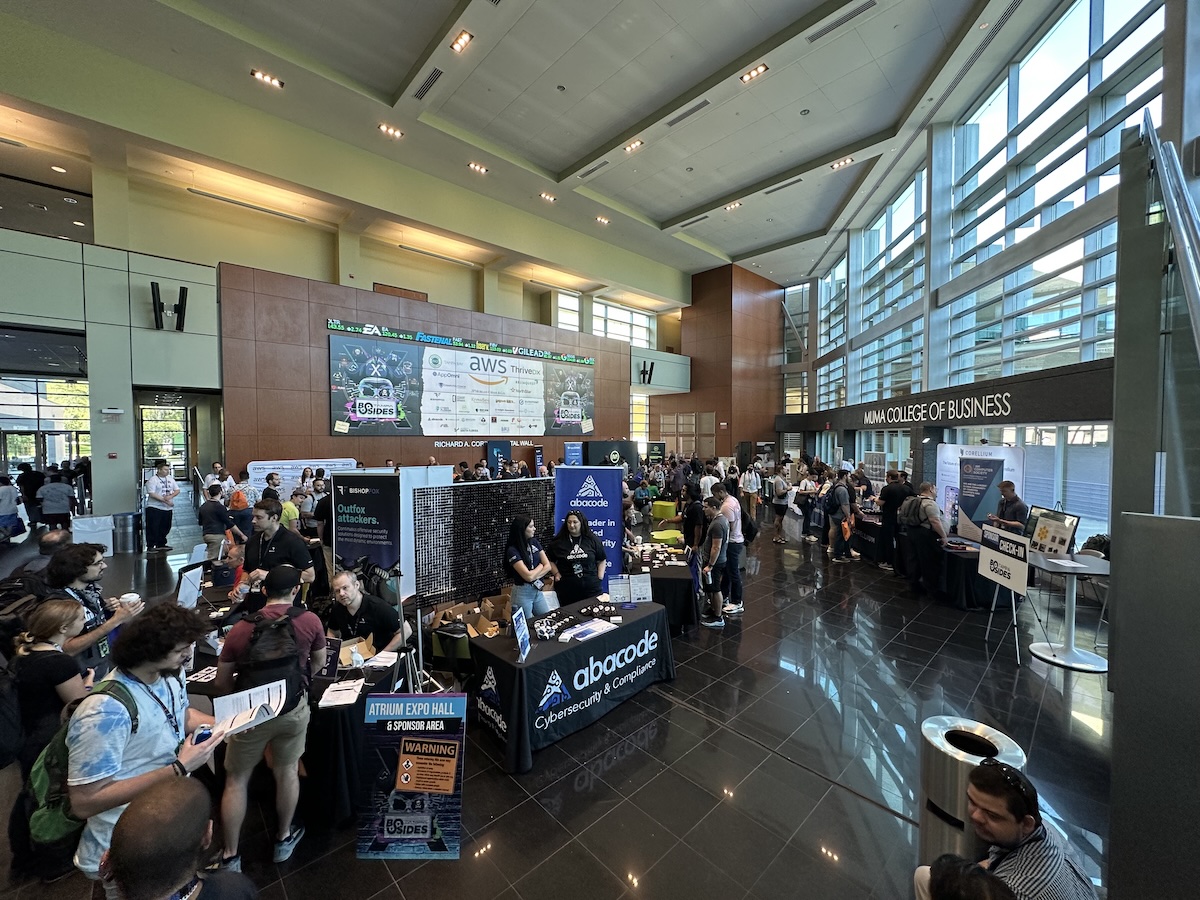
BSides Tampa 12, Tampa’s big cybersecurity conference, takes place this weekend at the University of South Florida!
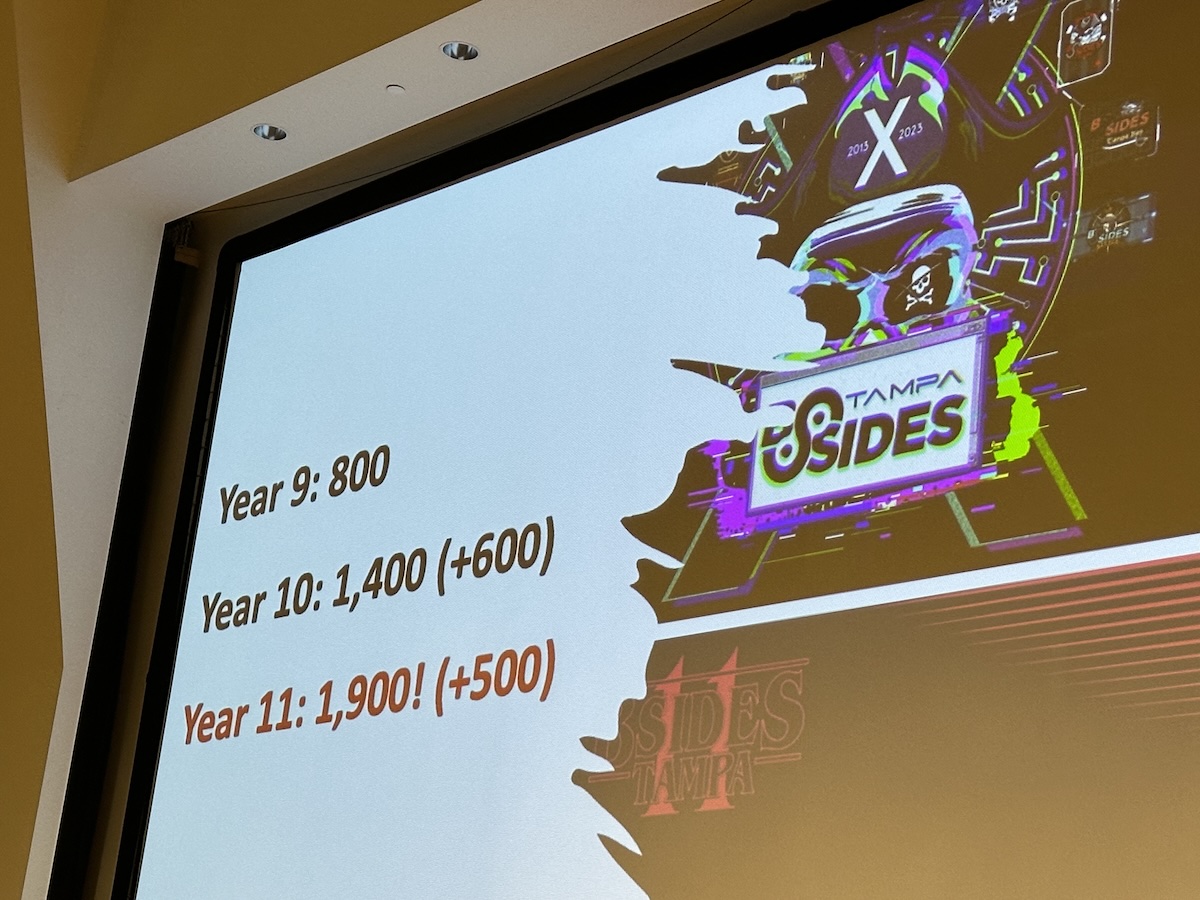
BSides Tampa is one of Tampa Bay’s biggest tech conferences, with 1,900 attendees at last year’s event:
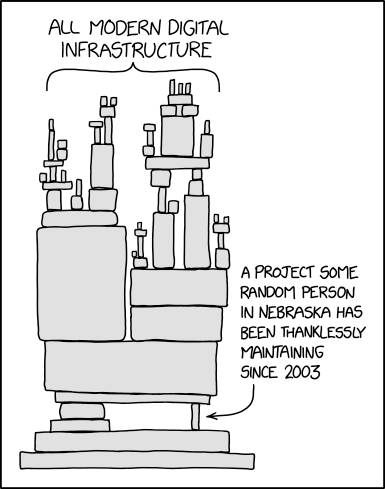
It’s worth checking out, even if cybersecurity isn’t your main focus. For starters, in today’s incredibly networked and AI-powered environment, security is everyone’s concern.
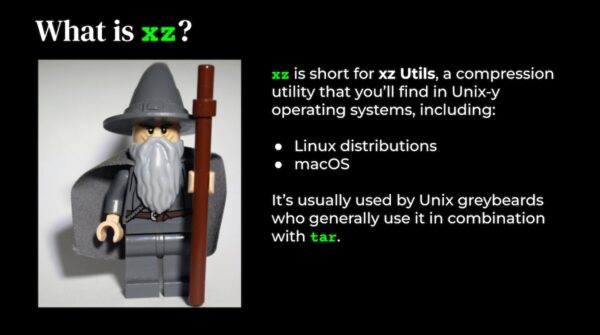
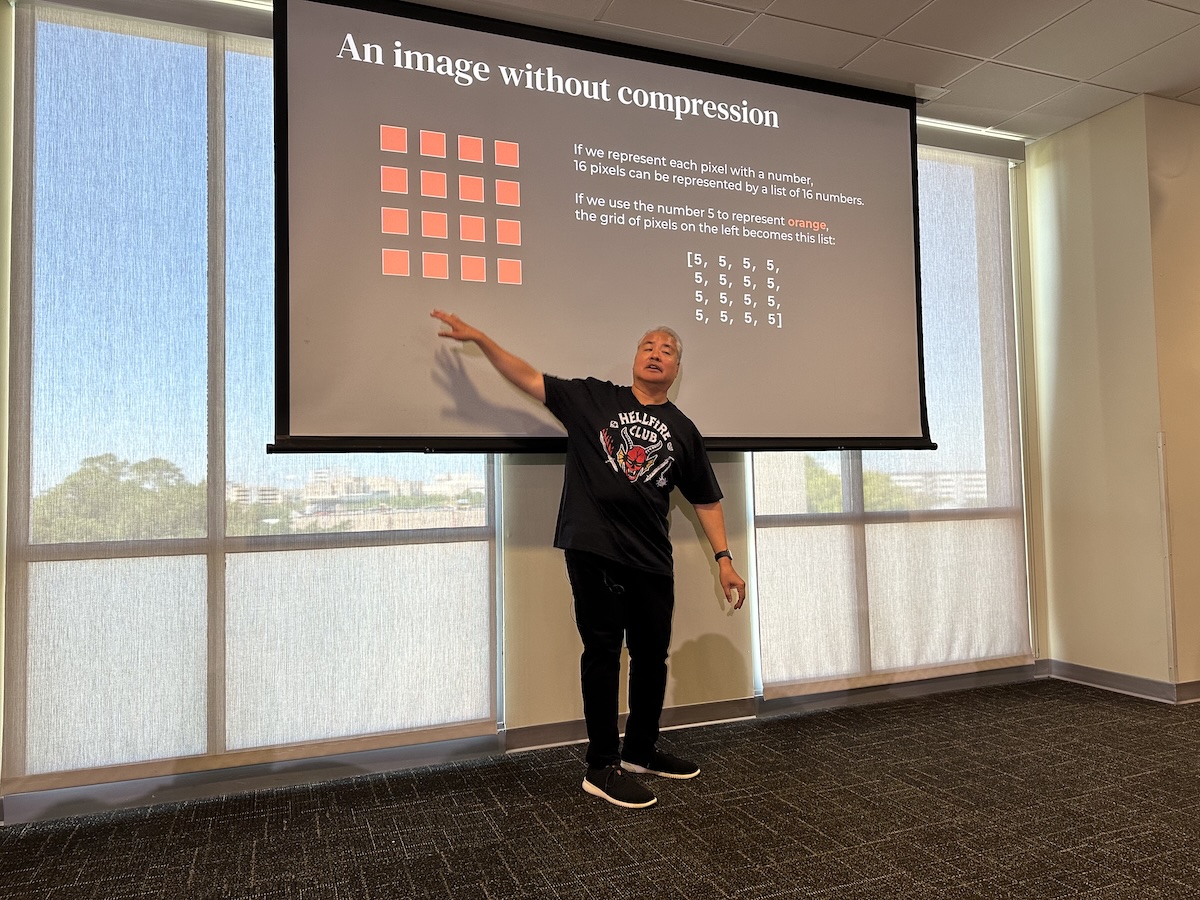
You’ll also learn a lot, whether it’s from one of presentations spread across seven tracks, the villages (the Social Engineering Adventure Village, the Lockpick Village, and the Network Security Village), the two Capture the Flag events, or the people you’ll meet.
BSides Tampa will take place over two days:
- Friday, May 16: Training and workshops
- Saturday, May 17: The main conference and post-conference happy hour
The tickets for the main conference are very reasonably priced:
- General admission: $45
- Students / active-duty military / veterans: $30
You can buy tickets to BSides Tampa here.
BSides’ history
BSides gets it name from “b-side,” the alternate side of a vinyl or cassette single, where the a-side has the primary content and the b-side is the bonus or additional content.
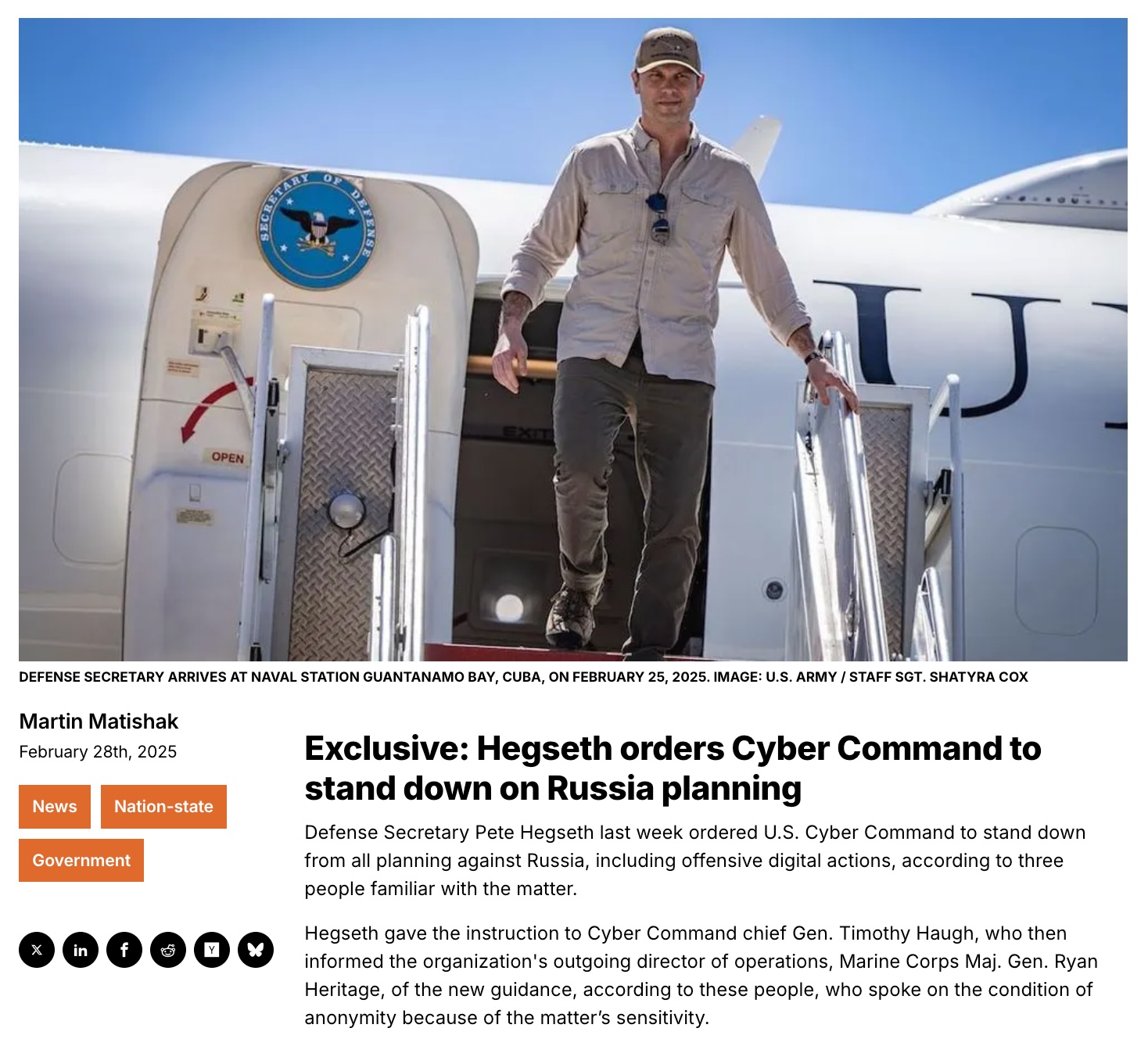
In 2009, the Black Hat conference in Las Vegas received way more presentation submissions than they could take on. The rejected presenters had very good presentations; there just wasn’t enough capacity for them. Those presenters, disappointed at not having their presentations accepted, banded together and made their own “b-side” conference in the spirit of Bender from Futurama.
That event was the first BSides, a small, hastily-assembled event that ran at a BSides organizer’s house at the same time as Black Hat on July 29 and 30, 2009.
Here are some photos:




Here’s the summary of that first BSides from the BSides history page:
It was a wild success: the talks were good, the party was better, and it was clear that the security community was excited at the idea of a conference that focused on conversations and personal interaction with peers. Those involved in the first event had a vision of rolling the idea out at a regional level, enabling local organizers to set up similar conferences in their own area.
In 2010, BSides took place again in Las Vegas, but there were also BSides conferences in Atlanta, Austin, Berlin, Boston, Dallas, Delaware, Denver, Kansas City, Ottawa, and San Francisco. In 2011, it would expand to over 40 events, with Africa and Australia joining the list of continents that had a BSides conference.

Tampa had its first BSides on February 15, 2014, and it’s grown over the years to become one of the biggest Tampa Bay tech events of the year.

 BSides Tampa is sponsored by the Tampa Bay chapter of (ISC)², which is clever and mathematically-correct shorthand for “International Information System Security Certification Consortium”. (ISC)² is a non-profit specializing in training and certifying information security professionals.
BSides Tampa is sponsored by the Tampa Bay chapter of (ISC)², which is clever and mathematically-correct shorthand for “International Information System Security Certification Consortium”. (ISC)² is a non-profit specializing in training and certifying information security professionals.
Join us at BSides Tampa this weekend!