Crypto
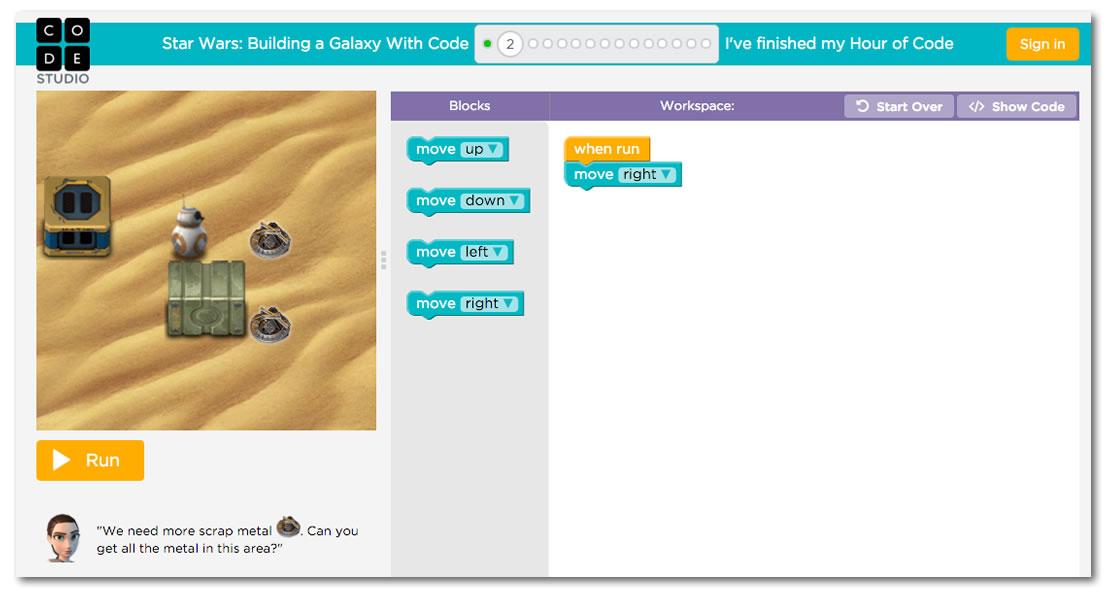
By now, you’ve probably heard that the FBI’s current fight with Apple, in which they’re trying to get the company to build workarounds for the phone’s security protections in order to be able to brute-force guess the iPhone passcode used by Syed Rizwan Farook, one of the suspects in the December 2015 San Bernardino shooting. The passcode isn’t just some piece of information you have to provide to gain access to an iPhone; it’s actually part of the key used to encrypt and decrypt iPhone memory contents, as shown in the diagram below:
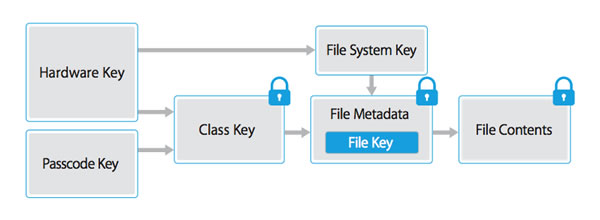
Apple key derivation, from Apple’s iOS Security Guide, September 2015.
iOS has a number of measures built in to make brute-force guessing difficult, including an optional setting that disables the phone after 10 wrong passcode entries and a mandatory delay between passcode entry attempts (which, for later phone models, grows in length with each failed attempt). The FBI believe that Farook turned the “ten strikes and you’re out” setting on the iPhone on, which is why they’re demanding that Apple provide a workaround.
Corbató’s Law

The FBI/Apple situation may have left you asking questions, but one question you might not have asked is “Who came up with the idea of using passwords to secure access to files?” With computer science being such a young field — the formal definition of computable didn’t appear until the 1930s, and the oldest programming languages are from the 1950s — many of its pioneers are still alive. This is the case with the lock-files-with-passwords creator, Fernando J. Corbató. In a 2014 interview with the Wall Street Journal, he said that the password system has become unmanageable these days.
Corbató has made many other contributions to our field that we benefit from even today, including:
- time-sharing, which he explained to a 1963 TV audience in this archival video,
- the Multics operating system, which introduced concepts such as hierarchical file system, ring-oriented security, access control lists, single level store, dynamic linking, and extensive on-line reconfiguration for reliable service, and inspired the development of Unix, and
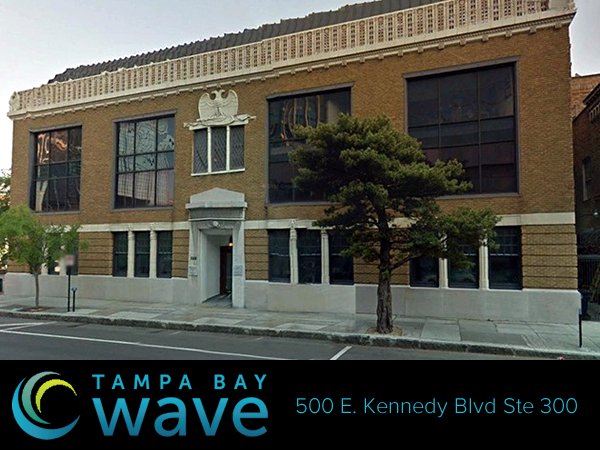
- Corbató’s Law, which is illustrated below:
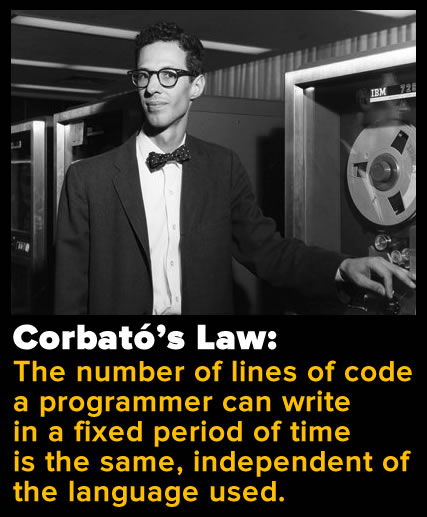
Simply put, what Corbató is saying is that every day, you only have so many lines of code in you. The corollary to Corbató’s Law is that for maximum productivity, you should use a programming language that lets you do things in as few lines as possible — a language that minimizes yak shaving.
Cartoons
The term “yak shaving” was first used in its programming sense at the MIT Media Lab around 2000, and likely comes from this episode of the ’90s cartoon series Ren and Stimpy:
As Jeremy Brown from MIT put it:
…yak shaving is what you are doing when you’re doing some stupid, fiddly little task that bears no obvious relationship to what you’re supposed to be working on, but yet a chain of twelve causal relations links what you’re doing to the original meta-task.
Many programming languages require you to do some amount of yak shaving, but one notorious culprit is also one of the most popular: Java.
Kotlin
 (In case you missed it, I wrote a little bit about Kotlin yesterday.)
(In case you missed it, I wrote a little bit about Kotlin yesterday.)
Here’s a simplified version of the dreaded class example you’re likely to find in a programming textbook: the Person class. It’s a data class — we’re really using a class as a structured record type, since Java doesn’t have any. This one has two fields that won’t change once instantiated: name, a string, and age, an integer value. Here’s the Java implementation:
public class Person {
private final String name;
private final int age;
public Person(String name, int age) {
this.name = name;
this.age = age;
}
public String getName() {
return name;
}
public int getAge() {
return age;
}
}
Here’s a Kotlin Person class that does everything that the Java Person class above does, but in one line as opposed to ten:
data class Person(val name: String, val age: Int)
Kotlin lets you specify a primary constructor on the very same line as the class keyword, and you can specify other constructors within the class with init. The val keyword defines name and age as write-once properties, which automtically provide getter methods. By annotating the class with the data keyword, you add all sorts of data class goodies like equals, hashCode, toString. Simply put, using Kotlin in place of Java means less yak shaving. I’m a little more interested in Android development now.