
Here’s what’s happening in the thriving tech scene in Tampa Bay and surrounding areas for the week of Monday, June 2 through Sunday, June 8, 2025!
This list includes both in-person and online events. Note that each item in the list includes:
✅ When the event will take place
✅ What the event is
✅ Where the event will take place
✅ Who is holding the event

This week’s events
- Monday, June 2
- Tuesday, June 3
- Wednesday, June 4
- Thursday, June 5
- Friday, June 6
- Saturday, June 7
- Sunday, June 8
Monday, June 2
| Event name and location | Group | Time |
|---|---|---|
| Business Networking Meeting Online |
Christian Professionals Network Tampa Bay | 11:30 AM to 12:30 PM EDT |
| Downtown St. Pete Business Networking Connection Lunch~ All Welcome< JOIN In! Carrabbas |
RGA Networking Professional Business Networking | 11:30 AM to 1:00 PM EDT |
| Sameer Saleem: Tech for Good Station 2 Innovation Center |
Entrepreneurs & Startups – Bradenton Networking & Education | 5:30 PM to 7:00 PM EDT |
| Speakeasy Toastmasters #4698 Online |
Toastmasters District 48 | 6:00 PM to 8:00 PM EDT |
| Monday Feast & Game Night Village Inn |
Tampa Bay Tabletoppers | 6:00 PM to 11:00 PM EDT |
| Weekly General Meetup Online |
Beginning Web Development | 8:00 PM to 9:00 PM EDT |
| Return to the top of the list | ||
Tuesday, June 3
Tuesday from 4 – 8 p.m. at Embarc Collective (Tampa): Tampa Artificial Intelligence Applications Meetup Group will hold a Sales and Marketing Masterclass.
Find out more and register here.
Wednesday, June 4
Wednesday from 5 – 7:45 pm at Accusoft: Tampa Devs presents Building Accessible Web Apps: Practical Solutions for Inclusive Design.
In this session, you’ll learn how to identify common accessibility pitfalls and implement practical strategies to overcome them. Discover tools like axe DevTools and eslint-plugin-jsx-a11y, explore best practices for keyboard navigation, focus management, and ARIA roles, and see how accessible component libraries can simplify your work. By the end, you’ll have insights to build web apps that are not only functional but truly accessible, so everyone can enjoy!
Find out more and register here.
Thursday, June 5
Thursday at 5:30 p.m. at Tampa Bay Brewing Company (near Oldsmar): Join the Tipsy Techies Happy Hour for an exclusive evening of pure networking! This event is all about meaningful conversations and building valuable connections with fellow tech professionals and industry leaders.
Find out more and register here.
Thursday from 6 – 8 pm at Cigar City (Tampa): Tampa M365 and Tampa Power Platform are holding a social gathering at Cigar City! Enjoy beers, socialize, and network with awesome local techies. Whether you’re new to Microsoft 365 or an experienced M365 IT Pro / Developer, or new to Power Platform or an experienced Citizen Developer, this event is a great opportunity to meet new faces and get to know your local counterparts.
You can find out more and register on either the Tampa M365 meetup page or the Tampa Power Platform meetup page.
Thursday at 7 pm at Neon Temple (Tampa): Jon “Cochise” Buzin will deliver a talk called Surviving Helene and Milton: Lessons Learned and an Intro to Bugging In. Want to know how to make it through the next hurricane? You’ll want to catch this.
Friday, June 6
Saturday, June 7
Sunday, June 8
| Event name and location | Group | Time |
|---|---|---|
| Venice Strategy Board Gamers Venice |
Board Games and Card Games in Sarasota & Bradenton | 12:00 PM to 6:00 PM EDT |
| Board Game Flea Market and $1 Auction Tampa Bay Bridge Center |
Tampa Gaming Guild | 1:30 PM to 4:00 PM EDT |
| Sew Awesome! (Textile Arts & Crafts) Tampa Hackerspace West |
Tampa Hackerspace | 5:30 PM to 8:30 PM EDT |
| Return to the top of the list | ||

About this list
How do I put this list together?
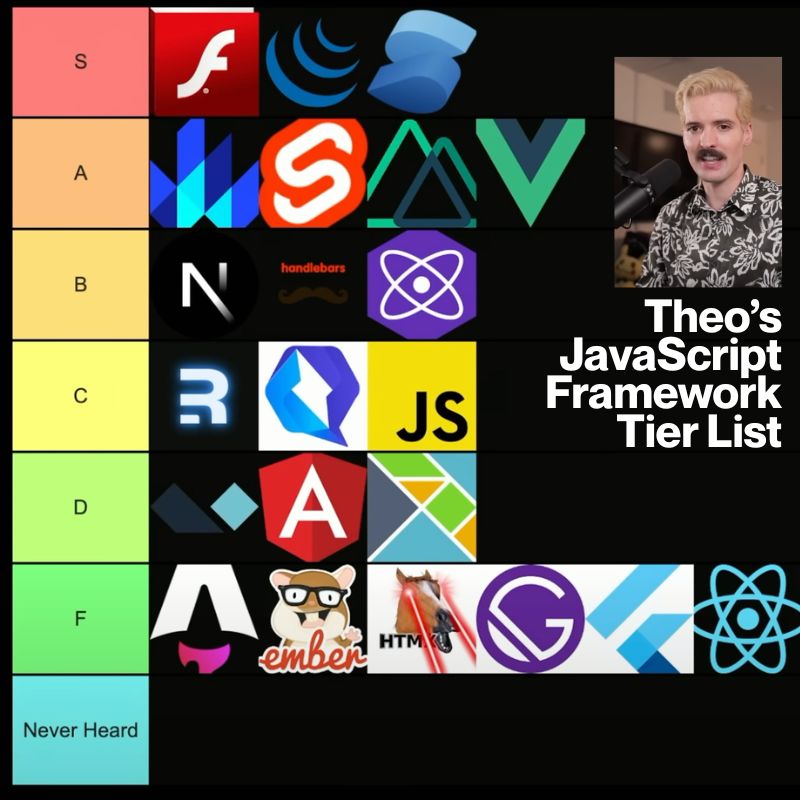
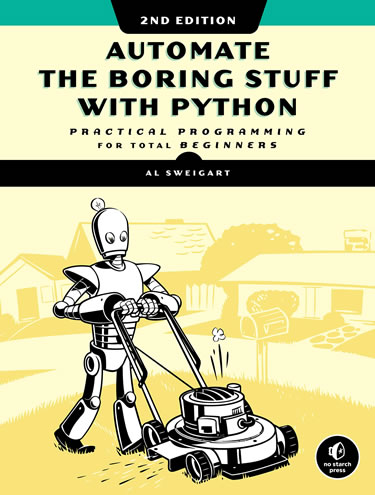
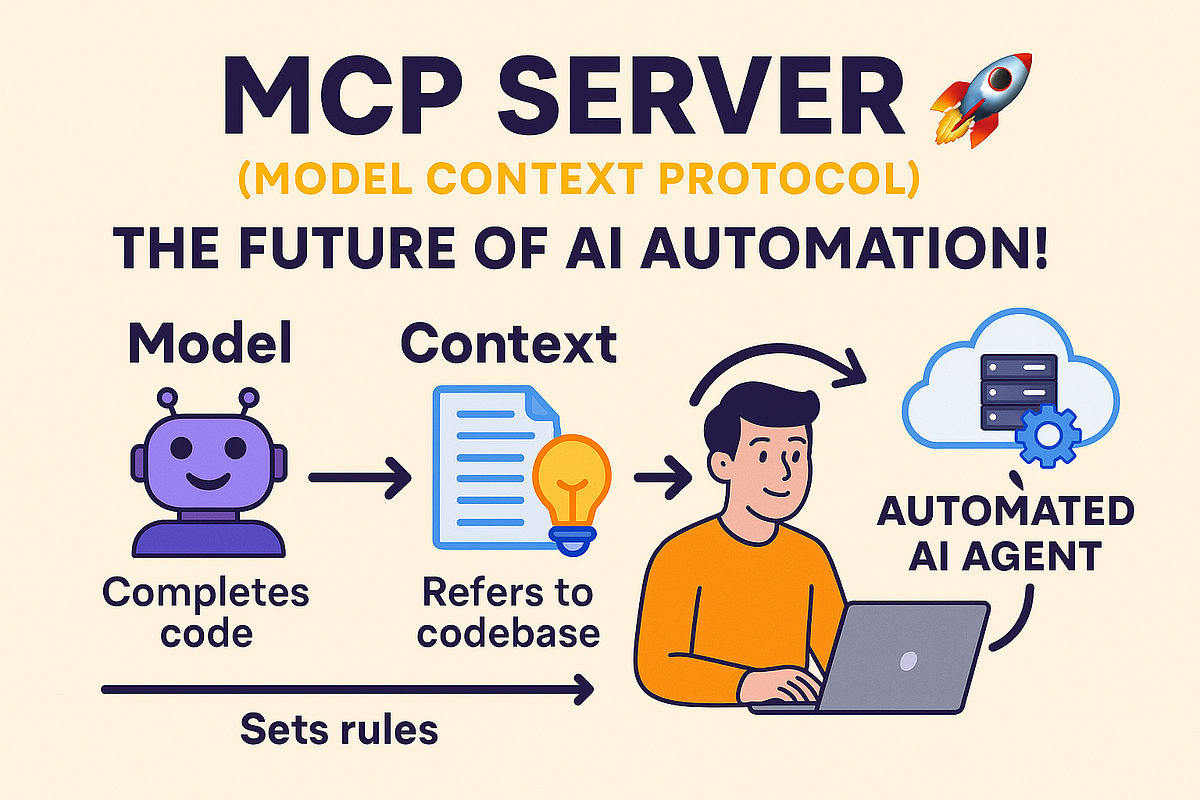
It’s largely automated. I have a collection of Python scripts in a Jupyter Notebook that scrapes Meetup and Eventbrite for events in categories that I consider to be “tech,” “entrepreneur,” and “nerd.” The result is a checklist that I review. I make judgment calls and uncheck any items that I don’t think fit on this list.
In addition to events that my scripts find, I also manually add events when their organizers contact me with their details.
What goes into this list?
I prefer to cast a wide net, so the list includes events that would be of interest to techies, nerds, and entrepreneurs. It includes (but isn’t limited to) events that fall under any of these categories:
-
- Programming, DevOps, systems administration, and testing
- Tech project management / agile processes
- Video, board, and role-playing games
- Book, philosophy, and discussion clubs
- Tech, business, and entrepreneur networking events
- Toastmasters and other events related to improving your presentation and public speaking skills, because nerds really need to up their presentation game
- Sci-fi, fantasy, and other genre fandoms
- Self-improvement, especially of the sort that appeals to techies
- Anything I deem geeky














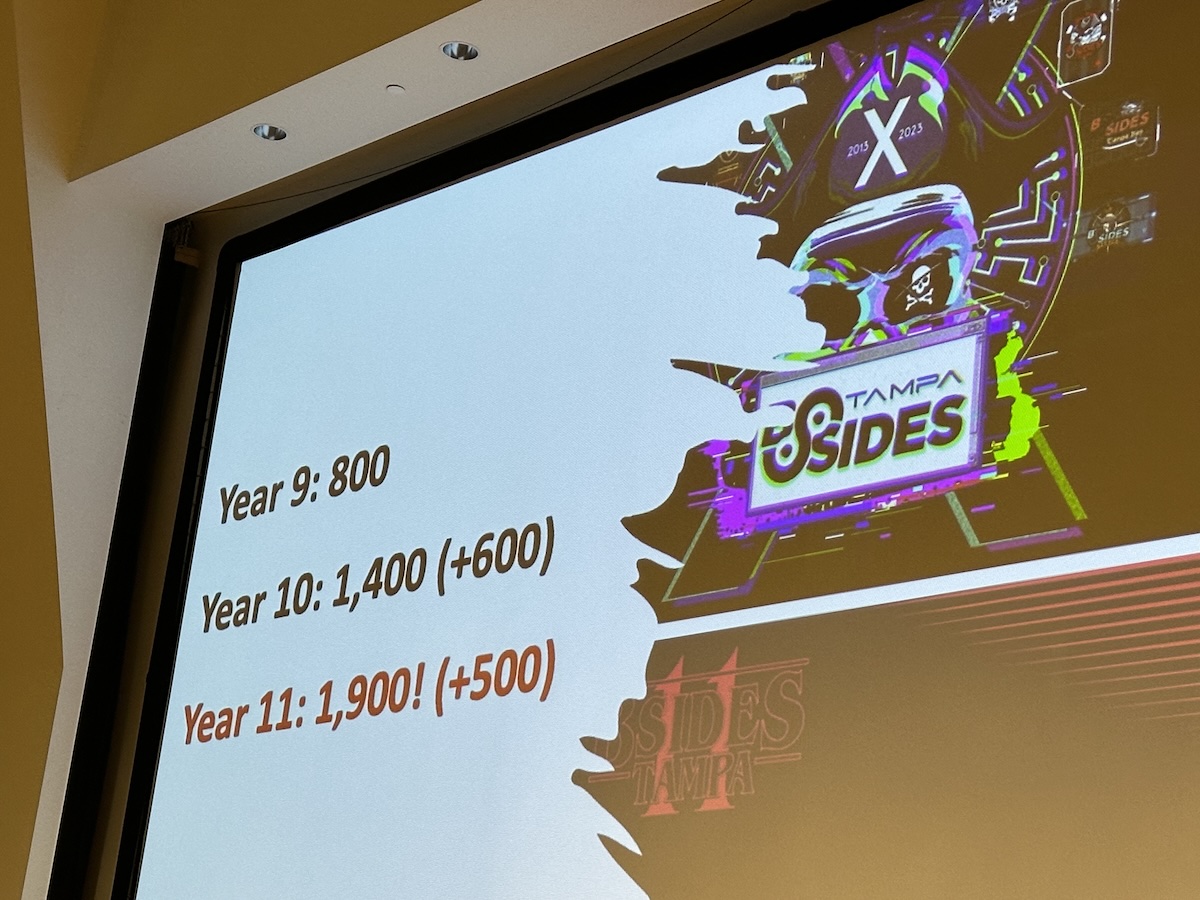
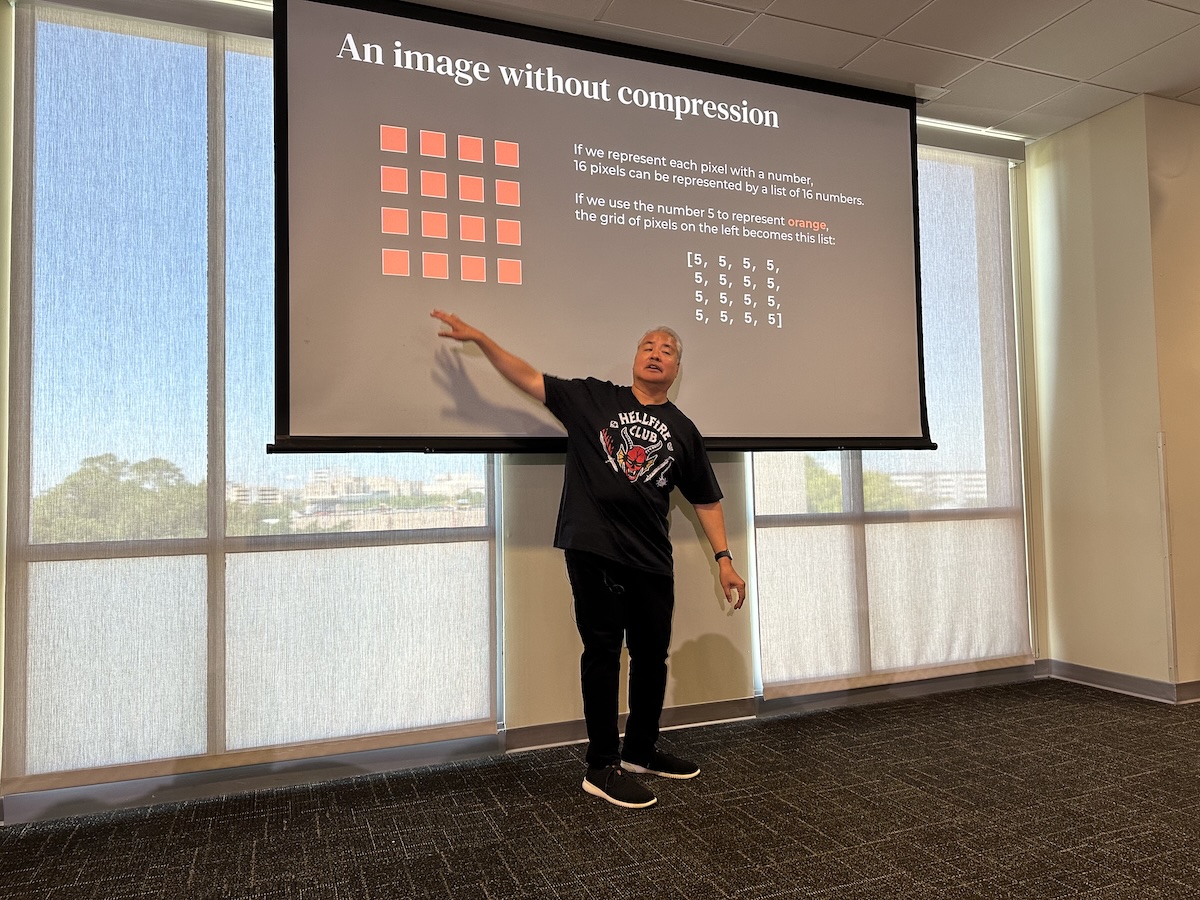














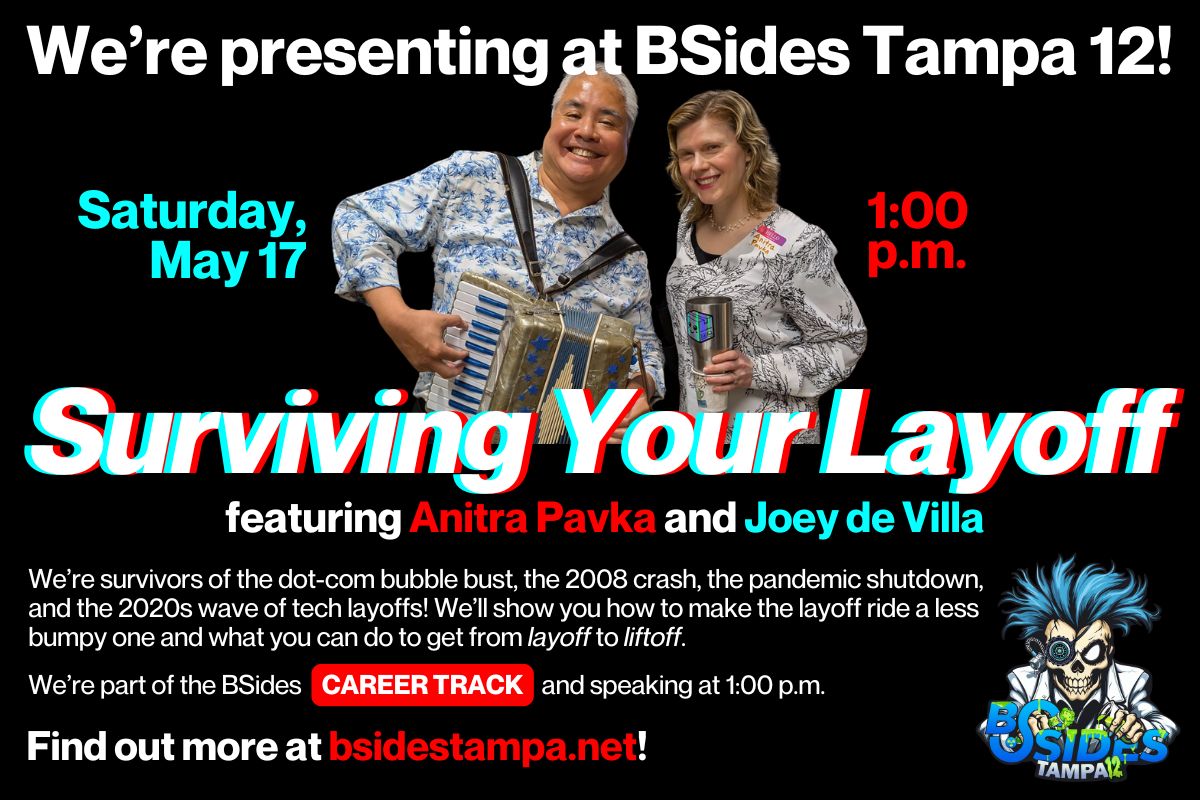 One of the talks at BSides is mine and
One of the talks at BSides is mine and 