Ereaders Losing Out to Tablets
GeekWire reports that the tablet is “killing the e-reader”. They cite an IHS report titled Ebook Readers: Device to Go the Way of Dinosaurs?, which reports that shipments of ereaders will be just under 15 million units by the end of the year, a 36% drop from the end of 2011, when they were over 23 million.
According to IHS, tablets are doing quite well:
In contrast, tablets are enjoying unstoppable growth, mostly thanks to the Apple iPad, which made its appearance in 2010. Tablet shipments will hit 120 million units in 2012 only after two short years of the device being on the market, and 340 million systems are expected by 2016—a magnitude of sales exceeded just by mobile handsets.
It seems that tablets are pretty good ereaders, in addition to being capable of doing a lot of things that used to be the sole province of multimedia-capable computers. The three areas in which ereaders have traditionally surpassed tablets are being eroded as well:
- Size: With tablets like the iPad mini and the Nexus 7, the small-size advantage that ereaders enjoyed is going away. The Kindle Fire HD is Amazon’s answer to this challenge: as tablets get smaller and more ereader-like, the Kindle Fire HD is an ereader that got more powerful and tablet-like.
- Price: Tablets are getting cheaper, especially the Android ones. With 7″ Android tablets dropping below the $200 mark (a 16GB Nexus 7 sells for $199), ereaders have to lower their price points in order to remain attractive.
- Battery Life: The low power requirements of epaper and cheaper processors give ereaders a considerably longer battery life than any tablet. This is the one advantage that will ereaders will continue to have over tablets, given the current trend for tablets to get better processors and displays.
Owned by an Angel
Justin Angel and Yours Truly. Photo by John Bristowe.
I know Justin Angel from my Microsoft days — he was a Silverlight engineer and I was a developer evangelist. He’s now with Nokia and is naturally working on Windows Phone, which leads me to wonder why he wrote an article on his site explaining how to get around in-app purchases, upgrade apps from trial mode to full-on mode without paying, and get rid of in-app ads. His site is currently down; whether it’s because of reasons technological or corporate is anyone’s guess.
2012’s Top Mobile Vulnerabilities and Exploits
Dark Reading has compiler their list of the top mobile vulnerabilities and exploits for 2012. You should read the article for the full version; here’s the list of items:
- Twitter SMS spoofing (discovered by my former Shopify coworker, Jonathan Rudenberg!)
- Dirty USSD
- Android SSL/TLS woes
- Android NFC vulnerabilities
- Mobile man-in-the-middle attacks using Exchange
- Social and sharing authentication flaws
- Zitmo, a.k.a. Zeus-in-the-Mobile
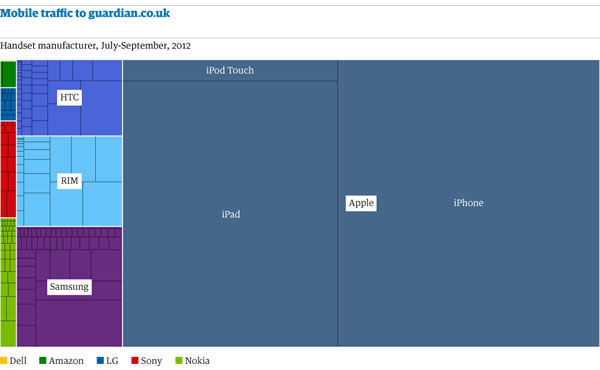
The chart above is from the Guardian article Fragmented world: what two years of traffic data teaches you about mobile. In 2010, Apple devices were already accounting for over half the Guardian’s mobile traffic; by 2012, they’re now accounting for about three-quarters. The Guardian serves about 3.3 million page a day to mobile devices, not counting those served to their iPad-specific app.
DevOps Best Practices for Cross-Platform Mobile Apps
This video features IBM’s Sanjeev Sharma’s presentation, DevOps Best Practices for Cross-Platform Mobile Apps, which he gave last month at MoDevEast 2012. DevOps gets little love in the mobile world, and I’m glad to see Sharma explaining its importance as well as showing some good techniques.
This article also appears in Mobilize!: The CTS Mobile Tech Blog.



2 replies on “Mobile Developer News Roundup: Ereaders Losing to Tablets, Cracking Windows 8 Games, 2012’s Top Mobile Vulns and Sploits, DevOps Best Practices”
[…] This article also appears in Global Nerdy. […]
OMG, I wish I’d seen this in July. Best advice ever. And it applies as well to single platform mobile developers.