It’s been a long-standing tradition in the tech press to make predictions for the next 12 months at the start of a new year, and they’re not about to break with tradition. We decided to do a roundup of predictions for the world of mobile tech made by some of the big tech news outlets and technology vendors, with our summary and take on what they think will happen this year. This is the first of two parts, and we make no guarantees as to whether or not they’ll come true. Rather, we feel that they’re valuable not for their accuracy, but as a source of insight into their thinking.
CNET’s Top 10 Predictions for the Mobile Market in 2014
CNET’s focus is on technology and consumer electronics news, so it’s no surprise that their predictions are about just two topics: the wireless carriers, and mobile device vendors. The one unifying theme of their 2014 predictions is that the vendors, whether for wireless service, smartphones, or tablets, will be competing even harder for your dollar.
 Carriers will pay more attention to the “value segment” of the market and offer more pricing options, especially for the budget-sensitive.
Carriers will pay more attention to the “value segment” of the market and offer more pricing options, especially for the budget-sensitive.- They’ll also lobby hard in Washington in anticipation of the upcoming auction for pieces of the AWS-3 spectrum, a range of frequencies formerly used by the Department of Defense, but now freed up for commercial mobile services. Simply put, access to mor frequencies means more data carrying capacity, and that’s something carriers will fight tooth and nail for.
- More carrier mergers and acquisitions, or at least attempts at them.
- T-Mobile will continue following their “uncarrier” strategy: eliminating contracts for personal accounts and roaming charges for more than 100 countries, removing device subsidies, letting people upgrade early, and giving away free data. It doesn’t hurt that their CEO, John Legere, has become a bit of a hero of the little people, what with trash-talking about the competition and gate-crashing their parties.
- Sprint emerges stronger from its rebuilding year, after going through a painful, but necessary process of replacing old infrastructure and getting LTE set up.
- Things will get worse at BlackBerry before they get better. They’ve got defecting customers and a tarnished image, but they’ll also come out with new devices for emerging markets (built by Foxconn) and a new focus on the enterprise.
- Microsoft will kill the Lumia brand and simply sell devices with the now-absorbed Nokia’s design and mobile knowhow.
- Apple and Samsung will continue duking it out in the courts.
- Unlocked phones will become mainstream, what with plans that encourage customers to take their phones with them as they switch carriers and notifying customers when their devices are eligible to be unlocked.
- LG up, HTC down. LG will reemerge as the hot Android device maker, after having built two excellent Nexus devices for Google, receiving critical (if not yet commercial) praise for the G2, and their general good performance in the home electronic markets. At the same time, HTC, despite having made the excellent HTC One, is facing difficulties and doesn’t have the size or reserves to endure a long down period.
Network World’s 12 Big BYOD Predictions for 2014
If you had to sum up Network World’s predictions for BYOD in a single sentence, it’s “Change is coming, and it’s going to be a pain in the corporate hindquarters.”
 COPE (Company-Owned, Personally-Enabled) devices will become more popular. Employees don’t really want to foot the bill for devices that they use at least partially for work, and the COPE model allows for both more complete device control and personal use.
COPE (Company-Owned, Personally-Enabled) devices will become more popular. Employees don’t really want to foot the bill for devices that they use at least partially for work, and the COPE model allows for both more complete device control and personal use.- BYOD will go beyond just smartphones, but extend to tablets and even laptops as employees, particularly millennials, prefer to choose and customize their own devices. Forrester analyst David Johnson observed the trend in 2013, and expects it to continue into 2014.
- They predict a “BYOD security bombshell” for 2014, as malicious parties will find it too tempting a target with too many opportunities for exploitation. BYOD’s become big enough, yet is still to new to have fully-formed security tools and techniques.
- They also predict the end of stipends, even though they cite Forrester analyst David Johnson saying that they’ll increase. Network World says they’ll disappear because it’s an employer’s market right now, and companies have no incentive to provide many perks, while Johnson says that if BYOD expands to include tablets and laptops, stipends will grow to cover them.
- After a couple of years from evolving from gatekeeper to enabler, IT will spend 2014 shoring up networks and systems to make them secure for BYOD.
- It’s expected that IT departments will attempt to assert control over BYOD, leading users to revolt. This shouldn’t be surprising, as mobile devices (and back in the 1980s, the PC) were first brought in by “rogue workers” who felt IT moved too slowly.
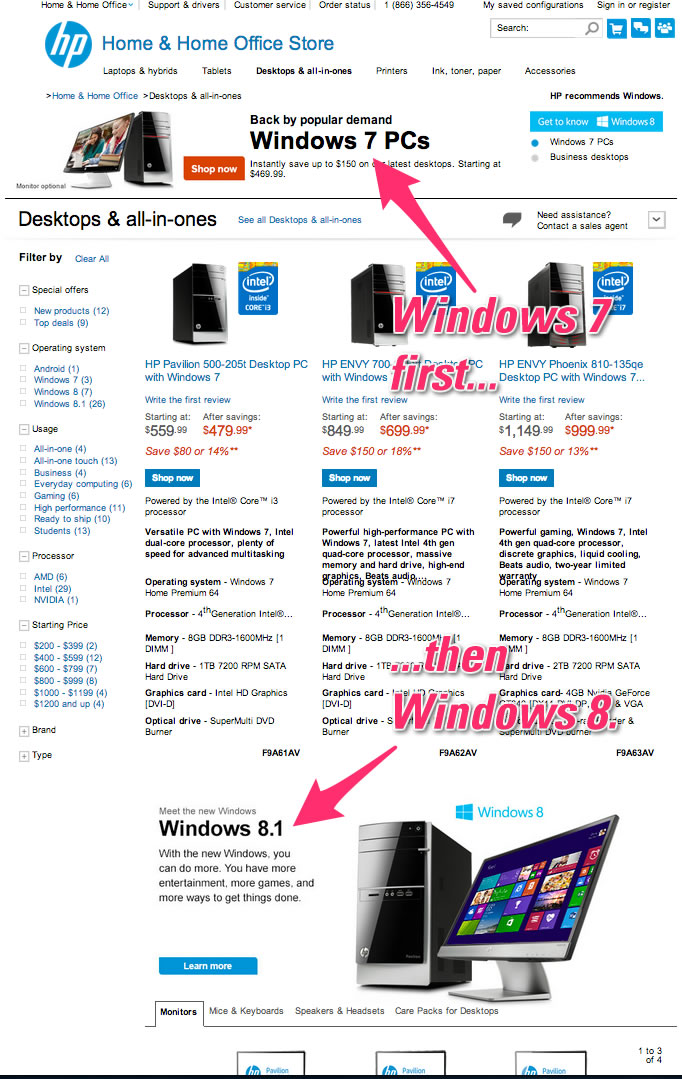
- A Microsoft tablet turnaround: according to a Forrester survey, while the iPad was the most-used tablet, when asked about BYOD tablet plans for 2014, Windows 8-based tablets were the most popular. We’ll have to see whether the actual outcome matches what the survey participants said.
- Mandatory BYOD gained momentum in 2013, and this led Gartner to predict that by 2017, half of businesses will require employees to provide their own phones for work. Network World expects that Gartner’s prediction will come true, and 2014 will see more companies requiring BYOD phones as a condition of employment.
- There will be even more competition in the MDM market, as more companies get into a market that grows more lucrative with the increasing adoption of BYOD.
- They predict the end of legacy apps, which rely on old browsers (especially IE 6 and 7), or are behind firewalls, or are dependent on desktop clients. As employees use mobile devices more and more, companies will move to SaaS (Software as a Service) to ensure that their applications can be accessed any time, anywhere.
- While companies have been working to make their applications accessible to mobile devices, not every bit of legacy software can be ported over. For these applications, virtual desktops are a good workaround, and Network World predicts that BYOD and the general use of mobile devices will give virtual desktops a new lease on life.
- “Wearables wreak havoc” is the way Network World phrases Forrester analyst J.P. Gownder’s prediction that wearable computing devices — smartwatches and the like — will take the enterprise by storm. It would seem that their attitude is “We’re still dealing with your mobile devices and you want us to take on something else too?”, and it’s quite possible that a lot of IT departments feel the same way. If that’s so, then the “rogue worker” prediction above will definitely come true.
Read Network World’s predictions
Ericsson Consumer Lab’s 10 hot consumer trends for 2014
The consumer lab division of Ericsson, who used to make mobile devices with Sony until 2012 (they still build the underlying technologies), prepared a booklet on their predictions for the hot consumer trends of 2014 for mobile technologies. Not only has a focus opposite that of Network World — consumer, rather than enterprise, but so is their more positive outlook. They do agree with Network World on one issue, however: change is coming.
 Just as PCs at work and home reached a large enough number to change the way we work, live and play, mobile devices will hit a number large enough to change everyday life and drive demand for a new set of services enabled by mobility. A number of areas of life, including shopping, restaurants, leisure facilities child/elderly care, communication with authorities and traffic, will be changed by offering services via mobile devices.
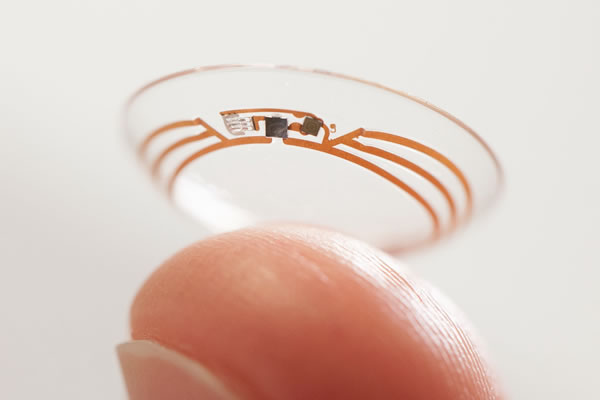
Just as PCs at work and home reached a large enough number to change the way we work, live and play, mobile devices will hit a number large enough to change everyday life and drive demand for a new set of services enabled by mobility. A number of areas of life, including shopping, restaurants, leisure facilities child/elderly care, communication with authorities and traffic, will be changed by offering services via mobile devices.- “Your body is the new password,” says Ericsson’s report, referring to the increasing use of biometric data, such as fingerprints, as passwords. Using fingerprints as passwords solves a few problems, but it introduces a whole new set, which we’ll cover in a later article. For now, let’s just say that there are reasons why security experts cringe whenever someone says they’ve solved the password problem with biometrics.
- The concept of “the quantified self” — the constant measurement of ourselves with technology — will become more popular. Thanks to GPS, smartphones can function as pedometers, apps that use a mobile device’s camera and wearable peripherals like the FitBit can track heart rate, and scales and other health devices like those made by Withings can send their readouts to mobile devices and computers. Mobile devices make it easier and more convenient to have a better gauge on our health, and such uses will become more prevalent.
- People will expect not just internet access everywhere, but a good connection as well.
- Thanks to smartphones, which are less expensive than full-blown PCs, the “digital divide” will be reduced, with more people worldwide having internet access. In developing countries, smartphones are often the primary internet device for most users.
- In spite of the various privacy and security issues (including the recent breaches at Target and Neiman Marcus), most people will still feel that the benefits of going online will outweigh those concerns. Rather than avoid making use of online services entirely, Ericsson’s Consumer Lab reports that 93% of the people they surveyed would rather be cautious and follow a “risk mitigation strategy”.
- Social networks will play a greater role in determining what people watch online, and much of those recommendations will be driven by influencers. According to Ericsson, 38% of the people they surveyed watched videos recommended by their friends several times a week, but only 22% recommended videos to friends several times a week.
- People will want to know how much mobile data they’re using, to better manage their mobile devices and mobile spending. 37% of smartphone owners use apps to test their connection speed, and 48% use apps to measure their data consumption.
- Sensors everywhere: with more interactive services will come the demand for our surroundings to become just as responsive through sensor-based services such as doors and gates that recognize you and automatically unlock (we’ve had this on newer cars for some time now). There are privacy concerns: more than a quarter of smartphone owners were uncomfortable with the idea of store sensors that made recommendations based on purchases by people with similar profiles.
- More people will “time and space shift”, that is, watch a video in one place on one device, pause it, and then continue watching the video where they left off in a different place, and possibly on a different device.
Download Ericsson Consumer Lab’s report [1MB PDF]
Eric Schmidt’s 2014 predictions
Google’s executive chairman says “the trend has been that mobile is winning; it’s now won”. He’s certain that big data and machine intelligence — and its availability through mobile devices — will be a big disruption. He also talks about Google’s biggest mistake: missing the rise and importance of social media.
In the Next Installment…
…we’ll cover ReadWrite’s and Netbiscuits’ predictions for the mobile web, as well as Techspot’s and CIO’s forecasts for mobile technology.






 Cecilia Abadie made history last year as the first driver to be given a traffic ticket for driving while using Google Glass, based on the California traffic law that states that you can’t drive while watching a monitor. She was initially pulled over for speeding on Interstate 15, but when the officer saw that she was wearing Google Glass, she was issued a second ticket for “driving while glassing”.
Cecilia Abadie made history last year as the first driver to be given a traffic ticket for driving while using Google Glass, based on the California traffic law that states that you can’t drive while watching a monitor. She was initially pulled over for speeding on Interstate 15, but when the officer saw that she was wearing Google Glass, she was issued a second ticket for “driving while glassing”.