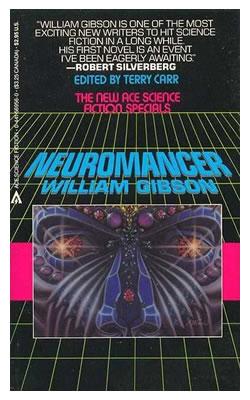
In his “Sprawl” series of short stories and novels, William Gibson made many references to World War III’s “cyberwar” component, especially in the novel Neuromancer. Willis Corto, an important character in that novel, is the sole survivor of a particularly important but forgotten operation in WWIII called Screaming Fist, which I’ll let Wikipedia summarize:
Operation Screaming Fist was an American military operation aimed at introducing a major virus into a Russian military computer. One of the main characters of the book, Corto, took part in the operation as a colonel. The operation was significant in that it involved dropping the team assembled for it by flying them across enemy lines on light gliders, with each member plugged into the first prototype cyberdecks. Unfortunately, the operation had been grossly mismanaged and had not taken into account certain aerial defenses. As a result, Russian EMP weapons were used against the gliders shortly after they entered Russian airspace. In the ensuing chaos, Colonel Corto escaped in a Soviet helicopter gunship and was the only survivor.
While it wasn’t as visually dramatic as soldiers and hackers on ultralights descending on a Russian military computer installation in a daring night raid, the denial-of-service attack on Estonia is just as Gibsonian, judging by the way the news outlets have been tossing about terms like “cyberattack”, “first war in cyberspace”, “cyberattack” and “digital Maginot Line.
What I find really interesting is that the only futuristic thing about the whole affair are the “cyber-” terms used to describe it. The actual attack itself isn’t anywhere as exotic or future-tech-y as Neuromancer and all those other cyberpunk novels of the ’80s and ’90s made such things out to be. In fact, a lot of it seems so damned ordinary:
| Cyberpunk stories | Real world |
|---|---|
| Cyber-attacks often required physical infiltration of a heavily-guarded site by a team comprising crack paramilitary troops and “console cowboys”. | The cyber-attack didn’t require anyone to physically go anywhere; it was all done online. |
| Cyber-attacks often required specialized viral software (“icebreakers” in Gibson’s novels, where “ICE” stood for “Intrusion Countermeasures Electronics”) that had to be written by AIs and were available only to the military or from specialized black market dealers like The Finn. | Cyber-attacks do make use of specialized viral software, but they’re written by humans — often teenagers with plenty of spare time — and are relatively easy to obtain if you hang around the right online circles (or wrong ones, depending on your point of view). |
Cyber-attacks were typically pulled off using very specialized hardware built by hardware gurus. Here’s a line from hardware specialist Automatic Jack from the short story Burning Chrome:
|
This cyber-attack was carried out by a botnet, which is essentially a lot of ordinary home computers — stock machines and “commodity hardware” — whose spare cycles are being harnessed by a virus that probably found its way in there via spam, malware site or some other rather ordinary vector. |
| Cyber-attackers interfaced with their machines by “jacking in”; that is, linking themselves to their machines through electrodes, through which they’d operate in a virtual reality-like environment.
If they ran into “Black Ice”, a deadly form of anti-malware countermeasures, their nervous systems would get fried. |
Cyber-attackers interfaced with their machines by “logging in”; that is, linking themselves to their machines through a keyboard, mouse and monitor, through which they’d operate in a command-line environment.
If they typed too long without a break, they’d get carpal tunnel syndrome and their wrists would get fried. |
| Cyber-attack targets were fancy-pants specialized computer installations accessible to few, such as military supercompters in Neuromancer’s backstory or the AI complex in its climax. | The cyber-attack target was the Estonian internet, which people used for everyday activities, from banking to email to looking at pictures of other people’s cats with funny captions. |
| Fashion: Many hackers wore leather, black jeans and mirrored shades. | Hey, this is also true in real life! Score one for Gibson! |
18 replies on “Cyberwar Ain’t What It Used to Be”
The actual attack itself isn’t anywhere as exotic or future-tech-y as Neuromancer and all those other cyberpunk novels of the ’80s and ’90s made such things out to be. In fact, a lot of it seems so damned ordinary:
I disagree! Gibson’s account of Op Screaming Fist sounds much more old-fashioned than the Estonia attack; it could almost be a slightly updated version of the WW2 Bruneval Raid or Op Gunnerside. Commandos actually parachuting in to the site (well, microlighting); gunfights; anti-aircraft fire… all very 1940s. In reality, we’re dealing with worldwide networks of hijacked computers, taking down not just a military computer but a country’s entire government! From anywhere on earth! Mobs of anonymous teenagers – real “cyber punks”, rather than crewcut Green Beret types – writing their own homebrew weapons, rather than stealing them from government armouries…
Much more unsettling and different than Gibson imagined.
From the viewpoint of the early 1980s, a lot of the things in the “real world” column are pretty science-fictiony. Botnets? Computer viruses available for free to anyone who looks for them? Malware? Spam? People carrying out their everyday lives over a computer network? Pictures of cats speaking l33t? Estonia?
Of course, Gibson’s early work (and that of his imitators) is also full of anachronisms. There are no cellphones. The USSR still exists (and is a powerful presence). A few megabytes of RAM is a hot commodity on the black market. It’s fiction, and nothing dates so quickly as the future.
@Colin: I was in high school back then, and I remember my Estonian classmate Erik talking about how the Reds had taken over his country, so I laughed out loud when I saw Estonia in your list of things that would’ve been considered science fiction back in the 1980s.
Cyber-attacks often required physical infiltration of a heavily-guarded site by a team comprising crack paramilitary troops and “console cowboys”.
The big difference here is that cyberpunks were after things on computers not connected to the net. When you’re after a secured system that’s guarded by armed troops, the street samurai come in handy.
@Colin –
Those megabytes were not RAM. They were “hot” data. Makes a bit of a difference.
“The cyber-attack target was the Estonian internet, which people used for everyday activities, from banking to email to looking at pictures of other people’s cats with funny captions.”
I CAN HAS CYBERBURGER???
For some sorts of cyber attacks you still have to get to the physical vicinity of the target. Attacks including interception of electromagnetic emissions (TEMPEST, wardriving) or tapping of cables or fiber optic still requires some wetware on-site.
Leather may look pretty but is impractical. Black jeans are maintenance-heavy. Fatigues and tactical vest – the more pockets the better – is the way of the Tao. Mirrorshades are optional.
The most elite folks build their own custom machines – or at least specialized coprocessors – from reconfigurable hardware. There is a corner in the future that belongs to the FPGA-like family of architectures. Far future will see the same on molecular level.
@Shaddack:
I always felt let down over how cybercrime turned out. No console cowboys, no custom-built computers, or even cool electrodes or wearable displays. Just some fairly regular people that can code and/or scam. No black leather either, more likely dirty cargo pants and a t-shirt. It is all so inglorious. At least there is still the mirrored shades.
FPGA’s (GPGPU anyone?) and specialized hardware (probably specialized crypto hardware in this case — bignum acceleration, PRNG’s, and the like) are the way to go. I can’t imagine doing any serious hacking in leather, though — too squeaky ;-P
http://kentsimperative.blogspot.com/2007/05/remembering-capabilities-centric-models.html
In the same manner, we note a fascinating analysis of the recent real world “cyberwar” involving Estonia and Russia, compared to its fictionalized counterpart from the dawn of the networking era…..
….What strikes us most about this comparison is the difference between the fictional vision of an advanced state-owned, platform and shooter heavy special operations mission – against the reality of a distributed, commercial off the shelf capabilities-centric event for which attribution, let alone intent, is difficult to characterize effectively.
Cyberwarriors are wearing BDUs, not leather. USAF is converting 8th Air Force into another major command, Cyber Command, standing up this summer. The Air Force recognises that the flipside of their network-centric way of warfare is increased network vulnerability.
So there will be guys in uniform dedicated to not just defending the milnets and civnets, but also developing offensive tactics as well. Gliders are probably not going to be involved. =)
More details are available in the text of SECAF Michael W. Wynne’s speech last November, to A C4ISR conference.
And Shaddack wins the thread. Joey DeVilla, I think what Shaddack may have meant by black jeans being maintenance heavy is that they fade easily if not initially pre-soaked in vinegar solution to preserve dye, and subsequently always washed in cold water, gentle detergent, etc. Or am I just living up to my name?
Could Gibson – or anybody else – have predicted that something as laughably obvious as a Nigerian 419 scam would still find people gullible enough to fall for it?
Hmmmm..
So the War has begun!!!!!
[…] read more | digg story […]
I saw the former chief strategist of netscape at the SECTOR conference and he presented on the cyber war threat. I had worked with Kevin Coleman before, but his presentation really impacted me. His inventory of cyber weapons included DEWs, TEDs, and self morphing/self encrypting malicious code. We are in serious trouble. Hackers of the world should unite and hit any country that launches a cyber attack!
I always figured in the future I could be a razorgirl. Hasn’t happened yet… :) I am more of a console cowboy/girl- don’t need augmentation! LOL. LOVE Neuromancer too- there was to be a graphic novel of it done by some guy who was in Heavy Metal magazine all the time. Never happened, I guess. Dang.