Here’s what’s happening in the thriving tech scene in Tampa Bay and surrounding areas for the week of Monday, May 25 through Sunday, May 31!
This list includes both in-person and online events. Note that each item in the list includes:
✅ When the event will take place
✅ What the event is
✅ Where the event will take place
✅ Who is holding the event

This week’s events
Monday, May 25
Tuesday, May 26
Tuesday at 5:30 at Hidden Springs Ale Works (Tampa): It’s the last Tuesday of the month, which means it’s time for TampaTech Taps & Taco Tuesday!
As always, it will feature:
Tech – Connect & network with tech industry peers
Taps – Enjoy 15% off your tab as a tech attendee
Tacos – A full taco bar… who doesn’t love tacos?!
No speakers, no presentations – just great conversations and a Raffle (because that’s way more fun! )
Find out more and register here.

Tuesday at 6 pm at Embarc Collective (Tampa): The Tampa Digital Mixer returns! It’s for e-commerce operators, remote workers, digital marketers, Shopify entrepreneurs, Facebook Ads pros and AI enthusiasts and start-up entrepreneurs — an evening of high-impact networking and actionable conversations in the heart of Tampa Bay.
Find out more and register here.
Wednesday, May 27
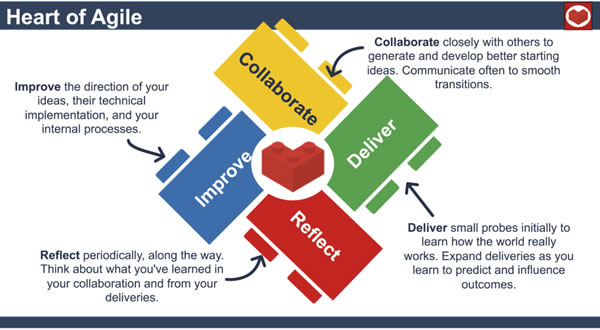
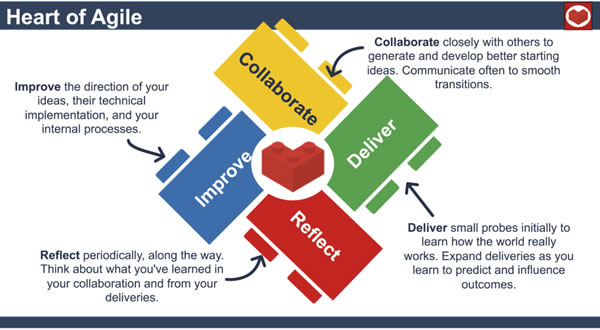 Wednesday at 12:30, online: Heart of Agile St. Pete – Tampa – Orlando presents an online Coffee Corner with the topicTalking to the People at the Top!
Wednesday at 12:30, online: Heart of Agile St. Pete – Tampa – Orlando presents an online Coffee Corner with the topicTalking to the People at the Top!
The description:
You know the moment. You’re explaining a delivery approach, surfacing a risk, or making the case for a better way of working — and somewhere mid-sentence, the leader across from you has already moved on.
Talking to the people at the top is one of the trickiest parts of doing Agile work well. The language doesn’t always travel, the priorities feel misaligned, and the stakes are real.
This session is an open, practitioner-focused conversation — no slides, no pre-work. We’ll use the Heart of Agile — Collaborate, Deliver, Reflect, Improve — as our lens for those moments. Just an hour on Zoom to swap honest stories about what has worked, what has fallen flat, and what those moments taught us.
You’ll leave with at least one concrete idea to try the next time you need a senior leader to understand what you’re doing and why it matters.
Bring a story. Bring a question. Coffee optional.
Find out more and register here.

Wednesday from 6 – 9 p.m. at Tiki Docks River Bar and Grill (Riverview): The West Florida chapter of ISACA, the global professional association for IT governance, cybersecurity, risk management, and assurance, is holding a Spring Networking Event at the Tiki Docks! Come and meet the folks behind the West Florida chapter and your fellow cybersecurity and tech professionals in a fun setting.
Find out more and register here.
Thursday, May 28
 Thursday from 4:00 – 6:30 p.m. at American Legion Post 138 (Tampa): It’s the May 2026 edition of the Tampa/ MacDill AFB Orange Call, Networking Event & Tech Round Table!
Thursday from 4:00 – 6:30 p.m. at American Legion Post 138 (Tampa): It’s the May 2026 edition of the Tampa/ MacDill AFB Orange Call, Networking Event & Tech Round Table!
In a military context, an “orange call” refers to an alert signaling a heightened cybersecurity state of readiness.
This orange call’s purpose is to gather and network amongst fellow communicators, guardians, and enablers of all ranks, titles, and experience levels, share resources and seek professional development. They will conduct an informal meet & greet and discuss MacDill communicators and missions, including the increasing role of cyber and the importance of defending our nation’s networks.
Find out more and register here.
Thursday from 6:00 p.m. at Entrepreneur Collaborative Center (Tampa): Data Analytics & AI Tampa Bay presents the May 2026 edition of their meetup, where experts present current trends and topics in the analytics field, including AI and ML, data science, business analytics, systems design, database management, data mining, and more!
Find out more and register here.
Thursday from 7:00 p.m. at Embarc Collective (Tampa): Tampa Devs presents XAI Evaluation: How to Know If Your Model’s Explanations Are Trustworthy, with Muntaser Syed!
Popular explainability methods like SHAP, LIME, and Integrated Gradients often yield conflicting results for the same model. How do you decide which one to trust? This hands-on workshop moves beyond “visual intuition” to introduce quantitative evaluation of XAI, providing objective tools to measure explanation quality.
Working through three interactive Google Colab notebooks, participants will:
- Identify Disagreement: Generate multiple explanations on real datasets to see exactly where and why they diverge.
- Apply Metric Frameworks: Measure explanations across three critical dimensions: Faithfulness (accuracy to the model), Robustness (stability), and Complexity (interpretability).
- Build Evaluation Pipelines: Create comparison tables and learn a decision framework for choosing explainers based on use cases like regulatory audits or stakeholder communication.
Find out more and register here.
Friday, May 29
Saturday, May 30
| Event name and location |
Group |
Time |
A Steampunk Murder Mystery in Tarpon Springs
Saturday, May 30 · 6:00 PM to 9:30 PM EDT |
Tarpon Springs Community Fun & Games |
7:15 PM |
THE REAL MEMORIAL DAY—HONOR, REMEMBER & ENJOY THE NIGHT!Saturday, May 30, 2026
Saturday, May 30 · 4:45 PM to 9:30 PM EDT |
Tampa (Citrus Park Area) Games Meetup Group |
1:25 PM |
Saturday Chess at Wholefoods in Midtown, Tampa
Whole Foods Market |
Chess Republic |
9:30 AM to 12:00 PM EDT |
EZ Stock (Stock, Options, Market)
2079 Range Rd |
Tampa Bay Technology Center |
10:00 AM to 12:00 PM EDT |
Plato’s “Republic” book 8.
North Sarasota Public Library |
Plato’s Republicans |
10:00 AM to 1:00 PM EDT |
The Fix – Coffee Chat
|
Palm Harbor late 20s early 30s Coffee Chatters |
10:00 AM to 12:00 PM EDT |
Ihop Board & Card Games Day
Ihop |
Geekocracy! |
11:00 AM to 2:00 PM EDT |
Twilight Imperium 4
Glitch’s House |
Board Games and Card Games in Sarasota & Bradenton |
11:00 AM to 9:00 PM EDT |
Friendship by Lydia Denworth
Felicitous (on 51st) |
The Culture Club – A Nonfiction Book Club |
12:30 PM to 2:30 PM EDT |
Electronics Soldering: Lesson I
MakerSpace Pinellas |
Makerspaces Pinellas Meetup Group |
1:00 PM to 2:00 PM EDT |
RPG Social Meetup
Mercado West |
St Pete and Pinellas Tabletop RPG Group |
1:00 PM to 3:00 PM EDT |
Youth Dungeons & Dragons Saturdays (Ages7-12) At Conworlds Emporium
Saturday, May 30 · 2:00 PM to 5:00 PM EDT |
Tarpon Springs Community Fun & Games |
1:00 PM |
FREE Fab Lab Orientation
Faulhaber Fab Lab |
Suncoast Makers |
1:30 PM to 2:30 PM EDT |
D&D (5e) @ Black Harbor Gaming (FULL)
Black Harbor Gaming |
St Pete and Pinellas Tabletop RPG Group |
1:30 PM to 5:30 PM EDT |
Wild Beyond the Witchlight (5e dnd)
Coliseum of Comics |
Adventurers of Central Florida |
2:00 PM to 6:00 PM EDT |
Saturday Chess @ Driftwood Kava & Roastery St. Pete
Driftwood Kava & Roastery St. Pete |
Chess Republic |
2:00 PM to 5:00 PM EDT |
Saturday Afternoon Catan
Whole Foods Market |
Tampa Bay Settlers of Catan |
4:00 PM to 7:00 PM EDT |
Board Brews
Zephyrhills Brewing Company |
Nerdbrew Events |
5:00 PM to 10:00 PM EDT |
Warmachine Journeyman League
Battlebrush Games |
Battlebrush Games: Paint Minis & Play Warhammer/Warmachine |
5:00 PM to 9:00 PM EDT |
Pathfinder D&D (Beginner to Experienced)
Descent Into Gaming |
Bradenton Roleplaying Games (RPGs) Meetup Group |
5:30 PM to 6:30 PM EDT |
Gaming Club: Reboot Hangout
Reboot Dunedin |
Dunedin-Palm Harbor Video Game Book Club |
6:00 PM to 8:00 PM EDT |
Community Hang-out Night
Online event |
Nerdbrew Events |
6:00 PM to 9:00 PM EDT |
Tampa Hackerspace Board Game Night
Tampa Hackerspace West |
Tampa Hackerspace |
7:00 PM to 10:00 PM EDT |
Yu-Gi-Oh Evening Tournament
Sunshine Games | Magic the Gathering, Pokémon, Yu-Gi-Oh! |
Sunshine Games |
7:00 PM to 11:00 PM EDT |
| Return to the top of the list |
Sunday, May 31

About this list
How do I put this list together?
It’s largely automated. I have a collection of Python scripts in a Jupyter Notebook that scrapes Meetup and Eventbrite for events in categories that I consider to be “tech,” “entrepreneur,” and “nerd.” The result is a checklist that I review. I make judgment calls and uncheck any items that I don’t think fit on this list.
In addition to events that my scripts find, I also manually add events when their organizers contact me with their details.
What goes into this list?
I prefer to cast a wide net, so the list includes events that would be of interest to techies, nerds, and entrepreneurs. It includes (but isn’t limited to) events that fall under any of these categories:
-
- Programming, DevOps, systems administration, and testing
- Tech project management / agile processes
- Video, board, and role-playing games
- Book, philosophy, and discussion clubs
- Tech, business, and entrepreneur networking events
- Toastmasters and other events related to improving your presentation and public speaking skills, because nerds really need to up their presentation game
- Sci-fi, fantasy, and other genre fandoms
- Self-improvement, especially of the sort that appeals to techies
- Anything I deem geeky